
필란드 보안업체인 에프시큐어(F-Secure) 에서 원격 데스크탑으로 전파되는 "Morto Worm" 이라는 악성파일에 대해 공개하였다.
현재 이 Worm으로 인해 TCP 3389 스캐닝이 증가한다고 있다고 SANS에서 발표하였다.
https://isc.sans.edu/diary.html?storyid=11452&rss
정확한 분석은 차후에^^
알약에서는 "Worm.Morto.A" 으로 탐지 될 예정이다.
- 원본보기 : http://www.f-secure.com/weblog/archives/00002227.html
We don't see that many internet worms these days. It's mostly just bots and trojans. But we just found a new internet worm, and it's spreading in the wild.
The worm is called Morto and it infects Windows workstations and servers. It uses a new spreading vector that we haven't seen before: RDP.
RDP stands for Remote Desktop Protocol. Windows has built-in support for this protocol via Windows Remote Desktop Connection. Once you enable a computer for remote use, you can use any other computer to access it.

When you connect to another computer with this tool, you can remotely use the computer, just like you'd use a local computer.
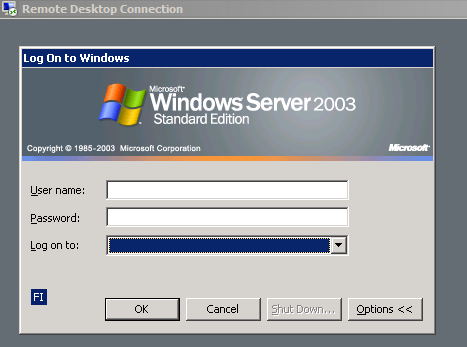
Once a machine gets infected, the Morto worm starts scanning the local network for machines that have Remote Desktop Connection enabled. This creates a lot of traffic for port 3389/TCP, which is the RDP port.
When Morto finds a Remote Desktop server, it tries logging in as Administrator and tries a series of passwords:
admin
password
server
test
user
pass
letmein
1234qwer
1q2w3e
1qaz2wsx
aaa
abc123
abcd1234
admin123
111
123
369
1111
12345
111111
123123
123321
123456
654321
666666
888888
1234567
12345678
123456789
1234567890
Once you are connected to a remote system, you can access the drives of that server via Windows shares like \\tsclient\c and\\tsclient\d for drives C: and D:, respectively. Monto uses this feature to copy itself to the target machine. It does this by creating a temporary drive under letter A: and copying a file called a.dll to it.
The infection will create several new files on the system including \windows\system32\sens32.dll and
\windows\offline web pages\cache.txt
Morto can be controlled remotely. This is done via several alternative servers, including jaifr.com and qfsl.net
We've seen several different samples. Some MD5 hashes include:
0c5728b3c22276719561049653c71b84
14284844b9a5aaa680f6be466d71d95b
58fcbc7c8a5fc89f21393eb4c771131d
More discussion on the topic at Technet forums.
We detect Morto components as Backdoor:W32/Morto.A and Worm:W32/Morto.B
'IT 보안소식' 카테고리의 다른 글
| "가짜 대검찰청 홈페이지"을 통해 개인정보를 가로채는 피싱(Phishing)사이트 주의 (6) | 2011.09.07 |
|---|---|
| 알약(ALYac), 알약 공개용 2.1 정식버전 출시!! (6) | 2011.08.29 |
| 안철수연구소(Ahnlab), TS(Total Security) 엔진 패치 안내 (0) | 2011.08.23 |
| 한국엡손(Epson), 고객정보 35만건 개인정보유출 해킹사건(8월 20일) (6) | 2011.08.20 |
| 안드로이드(Android), 정상 어플리케이션으로 위장하여 SMS를 발송하는 "DogWars" 어플 주의!! (4) | 2011.08.18 |




댓글